TL;DR: Modern cyber threats bypass single defenses. A layered security (defense-in-depth) architecture, combining identity, endpoint, network, application, data protection, monitoring and response, reduces single-point failures, limits attacker movement, and measurably lowers breach impact and cost. This post explains the concept, shows the research backing it, walks through a practical design and rollout roadmap, and gives an actionable checklist you can use today.
What is layered security (aka defense-in-depth)?
Layered security, often called defense-in-depth, is the deliberate application of multiple, diverse security controls across different layers of an environment so that if one control fails, others continue to stop, detect, or slow an attack. NIST describes it as layering heterogeneous countermeasures across common attack vectors so attacks missed by one control are caught by another.
Think of it like a medieval castle: walls, a moat, watchtowers, gates, and trained guards. Remove any single element and the castle is weaker; keep multiple elements and even sophisticated attackers face a sequence of hurdles.
Why layered security matters now, the research and numbers
Modern threat actors use diverse methods: credential theft, phishing, vulnerability exploitation, ransomware and third-party/supply-chain attacks. Recent industry studies show:
- The human element remains a major contributor to breaches, social engineering, phishing and misuse remain common initial entry points. In the 2024/2025 industry reports, a majority of breaches involve a human factor.
- Ransomware and vulnerability exploitation are top causes of system-intrusion breaches; ransomware accounted for a very large share of malware-related incidents in recent DBIR findings.
- The average cost of a data breach reached multi-million-dollar levels (reported global averages in 2024 around USD 4.45–4.88M), with costs rising due to lost business, downtime, and remediation. Layered controls that shorten detection and containment time materially reduce these costs.
Taken together: threats are many, attacks succeed via varied paths, and the financial stakes are high. A single firewall or antivirus is simply not enough.
Core layers of an effective layered-security architecture
Below are the common layers you should design for, each has a distinct role and purpose.
- Physical & Facility Controls
- Secure data centers, access badges, CCTV, environmental controls.
- Perimeter & Network Controls
- Next-Gen Firewalls, segmentation, IDS/IPS, secure VPNs. Network segmentation limits lateral movement when the perimeter is breached.
- Endpoint Protection
- EDR/XDR, application allowlisting, device hardening, patch management.
- Identity & Access Controls (IAM)
- Strong authentication (MFA), least privilege, role-based access, privileged access management (PAM). Identity is the new perimeter, NIST’s Zero Trust guidance emphasizes continuous authorization at the access level.
- Application & API Security
- Secure SDLC, SAST/DAST, runtime protection for web apps and APIs.
- Data Protection
- Encryption at rest/in transit, tokenization, DLP (data loss prevention).
- Supply-Chain & Third-Party Risk Management
- Vendor security assessments, contract clauses, software bill of materials (SBOM) where applicable.
- Monitoring, Detection & Response
- Centralized logging (SIEM), SOAR playbooks, 24/7 monitoring, threat hunting, incident response capability.
- Resilience & Recovery
- Backups (air-gapped where possible), business continuity planning, disaster recovery testing.
- People & Process
- Security awareness training, policy, change control, and tabletop exercises.
Each layer adds a distinct detection or mitigation capability; together they close gaps attackers exploit.
Design principles (how to think about layering effectively)
- Diversity of controls: Use different detection/mitigation approaches (e.g., behavioral EDR + signature AV). Homogeneous stacks fail together.
- Reduce single points of failure: Avoid relying on one control to stop an entire threat category.
- Least privilege & micro-segmentation: Reduce the blast radius if credentials are compromised.
- Assume breach / Assume compromise: Design so that an intruder can’t freely move or exfiltrate data after gaining an initial foothold (aligns with Zero Trust). (NIST Publications)
- Detect early, contain fast: Faster detection/containment correlates with substantially lower breach costs.
- Operationalize response: Playbooks, automation, and rehearsed processes are as important as tooling.
Practical roadmap: how an SME or mid-market org can adopt layered security
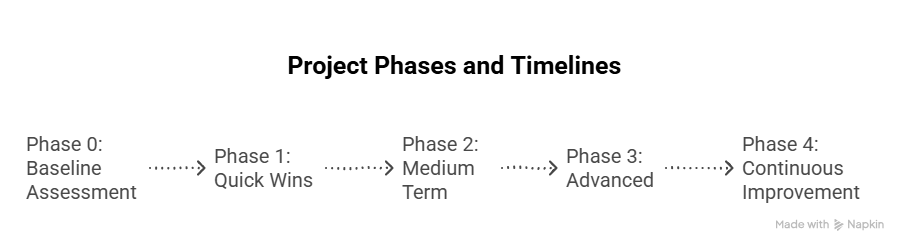
Phase 0 — Baseline assessment (2–4 weeks)
- Inventory assets, users, third parties, data sensitivity.
- Run a gap analysis against basic controls (MFA, patching, backups).
Phase 1 — Quick wins (1–3 months)
- Enforce MFA for all remote access and critical systems.
- Implement endpoint detection & response (EDR) on servers & user endpoints.
- Centralize logging for critical systems.
Phase 2 — Medium term (3–9 months)
- Network segmentation for sensitive environments (finance, HR, production).
- Deploy least-privilege access and start privileged access management for admins.
- Harden applications and introduce secure SDLC practices.
Phase 3 — Advanced (9–18 months)
- Move toward Zero Trust controls: continuous authorization, device posture checks, policy enforcement.
- Implement SOAR automation for containment workflows.
- Formalize supply-chain risk management and SBOM where applicable.
Phase 4 — Continuous improvement
- Regular tabletop exercises, red/blue/purple team engagements, and KPI tracking.
KPIs & metrics to measure effectiveness
Trackable metrics help justify investment and show improvement:
- Mean Time to Detect (MTTD) and Mean Time to Contain (MTTC), shorter times = lower cost.
- % of systems with MFA and % of privileged accounts under PAM.
- Patch cadence / Percent of critical vulnerabilities remediated within SLA.
- Number of security incidents vs. number contained automatically.
- Employee phishing click rate (post-training).
- Time to recover from backups / RTO (recovery time objective).
Benchmark quarterly and report to leadership, metrics drive behaviour.
Common pitfalls & how to avoid them
- Tool overload without integration. Buying many point products that don’t share telemetry creates blind spots. Solution: prioritize open telemetry (logs/alerts) and a central SIEM/SOAR.
- Treating security as a one-off project. Security is continuous. Build a roadmap and budget for recurring operations.
- Over-reliance on perimeter controls. Perimeters can be bypassed via stolen credentials or supply-chain flaws, bolster identity and endpoint layers.
- Ignoring third-party risk. Vendors can be weakest links, perform risk assessments and require security attestations.
Mini case example (anonymized, typical pattern)
A manufacturing mid-market company experienced credential theft via a targeted phishing campaign. They had a firewall and AV but no EDR, no MFA, and flat network access. Attackers moved laterally and encrypted critical systems.
After adopting layered security (MFA + EDR + network segmentation + daily backups + SIEM with automated containment playbooks), the next attempted intrusion was detected by endpoint telemetry, automatically isolated by EDR, credentials were rotated, and backups were used to recover encrypted assets, containment was measured in hours instead of days, and loss was minimized.
This illustrates how layers convert a catastrophic breach into a manageable incident.
Actionable checklist (what you can do in the next 30 days)
- Enforce MFA for all remote and privileged access.
- Enable centralized logging for servers and cloud workloads.
- Deploy or verify EDR on endpoints and servers.
- Ensure offline/air-gapped backups for critical systems, test a restore.
- Run a phishing-simulation and targeted security awareness session for staff.
- Identify the top 5 third parties and request evidence of their security posture.
- Create or update an incident response playbook and schedule a tabletop.
Why Ambsan helps
Layered security requires technology and operational maturity: integration of telemetry, tuning of detection rules, playbooks, and regular exercises. Many organizations benefit from a partner who can design the architecture, implement tooling, and run detection/response (MDR/SOC) so internal teams can focus on the business.
Secure Your Digital Ecosystem Today
Partner with Ambsan Technologies to build a future-ready layered security architecture.
Our experts specialize in cybersecurity, IAM, ERP integration, and IoT security, empowering businesses to operate securely and efficiently.
