Table of Contents
How Saudi Businesses Can Stay Safe from Cyber Threats in 2024
Why is Cyber Security important for businesses, particularly in Saudi Arabia, where cyber risks are increasing and causing significant issues? Safeguarding sensitive information, maintaining secure online systems, and ensuring adherence to regulations have become even more crucial as more companies embrace digitalization.
What is keeping your computer safe online? Cybersecurity is the set of steps and actions that are carried out to protect computers from threats that could damage or destroy businesses. We at Ambsan Technologies truly grasp these problems.
Our cyber security services help companies keep their digital presence strong and safe by protecting their networks, data, and potential risks. Let’s talk about it in detail:
The Importance of Cybersecurity for Saudi Arabia
Cyber security is the practice of protecting networks, systems, and data from cyber threats. Many Saudi Arabian businesses have recently started using digital platforms, so the need for good security has grown significantly.
There are many great possibilities in the digital world, but an organization needs to be aware of many risks. These risks could destroy operations, cause information to leak, or cause some other significant financial loss.
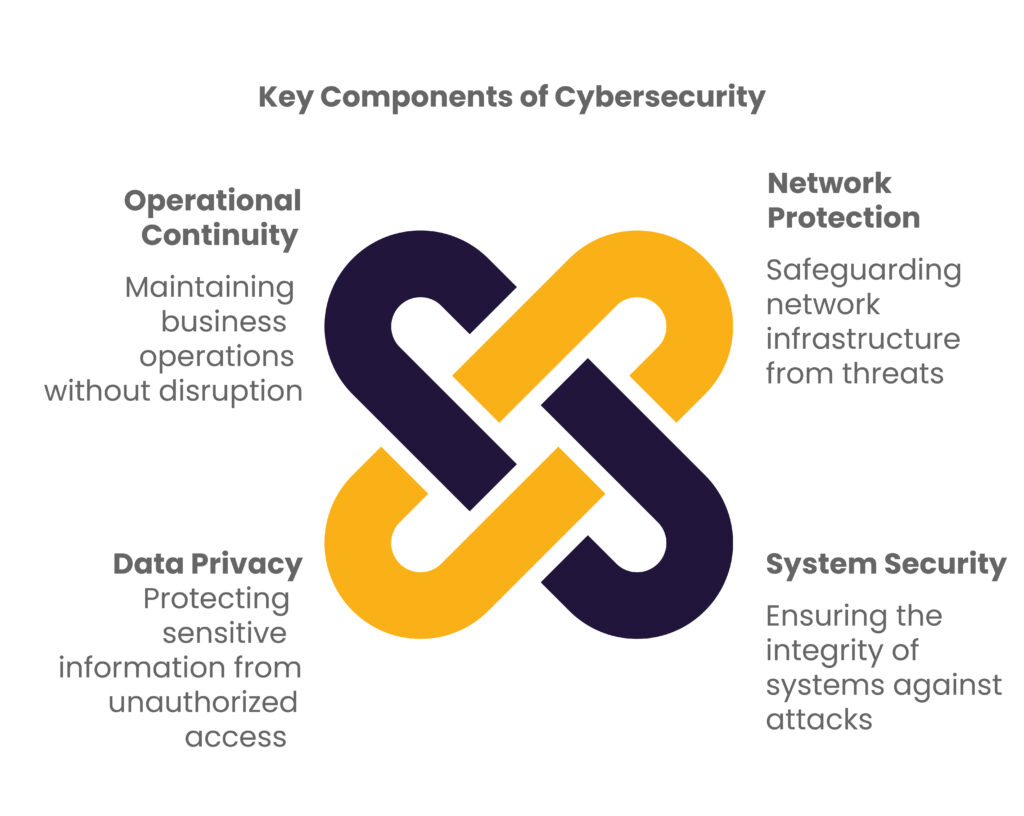
In this situation, cybersecurity is necessary to protect business assets’ accuracy, privacy, and availability. The following are some of the most essential parts of Internet security:
Data Safety
One of the most essential parts of cybersecurity is data safety. Financial records, customer information, and intellectual property are kept safe. Hackers who break into Saudi Arabian banks to steal personal and financial information must be stopped by using more substantial security technologies in their banks.
Network Security
There are ways to attack or misuse both internal and external networks. Networks should be protected from unauthorized entry, misuse, or privacy breaches. Typical defenses include firewalls, malware detection systems, and safe VPNs.
For instance, companies that deal with a lot of data, like healthcare organizations in Saudi Arabia, must keep their networks safe so that patient information can’t be accessed fraudulently.
Identity and Access Management
Identity and access management (IAM) limits what people in an organization can see and do. This minimizes insider risks or misuse by ensuring that only authorized users can access certain data or systems.
Saudi Arabian government agencies use other types of multi-factor authentication to ensure that only people who have already been checked out can access key infrastructure.
Application Security
Most cyber threats target weak spots in software programs. Businesses can reduce their vulnerability to attacks by keeping their apps updated and using the latest patches.
For instance, Saudi Arabian e-commerce sites should constantly update their apps to keep customer data safe so that people will continue to believe them.
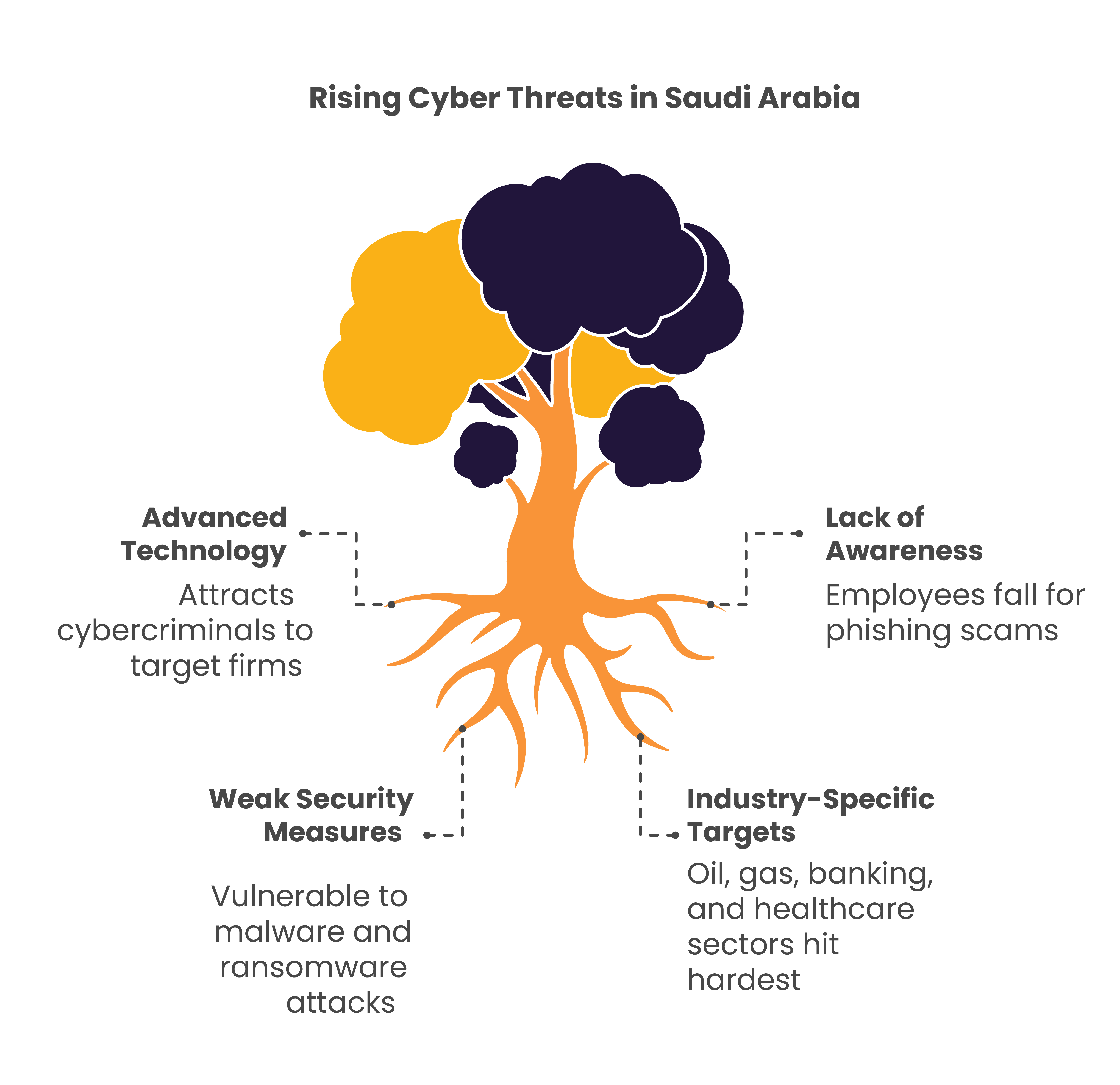
Common Cyber Threats in Saudi Arabia
Different cyber threats target Saudi Arabian companies because the country’s digital landscape is always growing. Due to its fast technological progress, Saudi Arabia is a popular target for cybercriminals.
This is because of its advanced technologies, such as e-commerce and cloud computers. Many organizations are affected by threats like malware, phishing scams, and ransomware because they are so common.
- Malware is one of the most common threats. It aims to get into systems and do damage by stealing private information or stopping activities. Several well-known malware attacks happened against Saudi companies, mainly in the oil and gas industry, causing them to lose money and time.
- Another major problem is phishing attacks, which use fake emails to get workers to give out private data like passwords or financial information. In the Kingdom of Saudi Arabia, phishing scams have targeted big and small companies, taking advantage of employees unaware of the company’s dangers and weak security measures.
- Ransomware is a new threat that locks hackers out of a company’s data and demands money to unlock it. In Saudi Arabia, the number of ransomware attacks has gone up. These attacks are mainly targeting private data in the banking and healthcare sectors.
Importance of Cyber Security Services
Digitalization is moving quickly these days, so cybersecurity services are something other than something special or fancy that businesses can use; they’re something that they must have. This is even more important in Saudi Arabia, where the internet proliferates and becomes more appealing to cybercriminals.
There are many cyber risks because more and more businesses are using digital technologies to make their processes faster, smoother, and more flexible, improve efficiency and productivity, and improve the customer experience.
Rising Saudi Cyber Security Demand
Saudi Arabia is one of the most connected countries in the Middle East to the Internet. Businesses and government agencies rely increasingly on these online tools to run their operations. This change is perfect for the economy but makes the country more vulnerable to advanced hacking.
For example, in 2017, one of the biggest cyber-attacks happened in Saudi Arabia. The government’s data was stolen, which hurt most industries a lot.
In this way, the attack made people wonder what kind of cybersecurity services the government and private businesses should use to avoid more disasters like this in the future.
Reasons Why Cyber Security Consulting Services Are Helpful
- Businesses that use cybersecurity consulting services get professional help tailored to their specific needs. Consulting services examine an organization’s infrastructure to find holes and suggest steps to lower dangers.
- Although a company may have strong internal security, it may still be open to threats in ways that the company isn’t aware of. Cybersecurity services solve these problems using their deep knowledge of the field and the latest security developments.
One Saudi Arabian bank that handles a lot of private customer data would greatly benefit from a full security audit by cybersecurity experts. Security experts could find holes in the system that hackers could use, like weak entry controls or old software versions that haven’t been updated.
After fixing these problems, the business will feel safe about its processes and its customers’ sensitive information.
Cyber Security Best Practices for Businesses in Saudi Arabia
Cyber threats will only get brighter as more businesses in Saudi Arabia use digital tools and technology. Since everything is going digital these days, companies need to have strong security measures in place.
As hacking targets businesses of all sizes, putting best practices in place for cybersecurity can keep your valuable assets safe from data breaches, which could mean closing your business. These are the most critical steps for companies in Saudi Arabia to take to protect their online safety:
Implement Strong Password Policies
Setting strict rules for strong passwords is likely the easiest and most effective way to fight online threats.
Workers can be told to create passwords that are hard to guess, using numbers, capital, and lowercase letters, and even special characters. Passwords should also be changed periodically to prevent people from gaining access without permission.
For example, businesses should use complex passwords like “S@uD!Business789” instead of easy ones like “password123” to make things even safer. Password managers store complex passwords safely so workers don’t have to remember each one, making things easier.
Authentication with Multiple Factors
Users must provide two or more proof factors before accessing accounts or systems with multi-factor authentication, which adds an extra layer of security. The proof factors can be something the person knows, like a password, something they have, like a phone that can get a one-time code, or something they are, like a fingerprint.
For instance, a business that handles private financial data might want its workers to log in using a password and prove their identity with an SMS code or a biometric scan.
Periodic Software Updates and Patching
Cybercriminals use gaps in old software or systems as opportunities to attack. A company should ensure that its systems, including operating systems, apps, and security software, receive regular changes that fix known security holes.
For instance, Ransomware attacks are easy to launch against a company that uses an old software version, like Windows, that no longer gets updates.
This is less likely to happen because its systems are regularly updated with security patches. Sometimes, encrypting data is the only way to tell the difference between success and failure.
Back-Up Your Data Often
Also, making regular backups of all critical data is very important in case of a hack, even one as bad as ransomware. This is important so companies can rebuild their systems and operations even after disasters without giving in to cybercriminals’ demands.

The Role of Cyber Security Training for Employee Awareness
Through computer training, employees will learn how to spot and deal with threats and how to inform others about such situations. Phishing, malware, and social engineering scams are examples of this activity.
In a typical phishing attack, a worker receives an email from a source they think they can trust, like a bank or a company boss, asking for private information like personal login information. If adequately trained, a worker could avoid falling into that trap and accidentally entering information that could risk your database.
- Employees can easily avoid these scams once they know the signs, such as misspelled email addresses, sketchy links, or urgent requests for private information.
- Training that simulates phishing attacks in a safe setting is an excellent example of how useful this training is. For example, a company might send workers fake phishing emails to help them spot a scam.
- By accurately showing people what phishing attacks look like and how to handle them, this practice finds holes in the organization and reinforces what they have learned in class. Working with real things can be much more helpful than just learning about them in a classroom.
- In addition, people are taught how to safeguard passwords appropriately. However, weak or repeated passwords have caused many data breaches.
- Companies might require their workers to make passwords with a mix of uppercase and lowercase letters, numbers, and special characters, and they would have to change these passwords often.
- During training classes, people can be shown how to use password management tools to safely store and create passwords, lowering the number of related security incidents.
How Cyber Security Services Help Protect Your Business
In an era where cyber threats are becoming increasingly sophisticated, investing in cybersecurity services is essential for safeguarding your business. These services are designed to protect your digital assets, ensure compliance, and mitigate risks associated with cyber attacks.
By partnering with a cybersecurity services company, businesses can access a range of solutions tailored to their specific needs, enhancing their overall security posture.
Cyber security managed services offer comprehensive protection by continuously monitoring and managing your security infrastructure. This proactive approach helps identify and address potential threats before they cause significant damage.
- For example, a managed cybersecurity service provider might employ advanced threat detection tools to monitor network traffic and detect unusual activities that could indicate a security breach. This constant vigilance ensures that potential threats are addressed in real time, minimizing the risk of data breaches and system outages.
Cybersecurity advisory services are critical in helping businesses develop robust security strategies. These services provide expert guidance on assessing and improving current security measures. For example, a cyber security advisory service might conduct a thorough risk assessment to identify vulnerabilities within your IT infrastructure and recommend best practices for enhancing security.
- For instance, they may advise implementing multi-factor authentication, strengthening password policies, and developing an incident response plan tailored to your organization’s needs.
Additionally, managed cyber security services can offer specialized solutions such as cybersecurity plan and event management (SIEM), which aggregates and analyzes security data across your network to detect and respond to potential threats.
These services include regular security assessments and compliance checks to ensure your business adheres to industry regulations and standards.
Cloud security is another area where cyber security services can significantly impact. Securing cloud environments has become a priority with the increasing adoption of cloud technologies.
Cyber security managed services can help protect data stored in the cloud by implementing encryption, access controls, and regular security audits. This ensures that sensitive information remains protected from unauthorized access and breaches.
Conclusion
One way to protect your business from online threats is to consider spending money on cybersecurity services. Options like cybersecurity managed services and advisory services can help you improve your defenses, ensure you’re following the rules, and lower the risk of security incidents.
At Ambsan Technologies, we offer a range of cybersecurity services to meet the needs of Saudi Arabian companies. We are here to help you whether you need full-service management, expert advice, or solutions tailored to solve specific problems.
Please don’t wait to contact us today to learn how we can help you improve your cybersecurity and keep your most important digital assets safe.
