In 2026, the traditional corporate “perimeter” in Pakistan has effectively dissolved. With the State Bank of Pakistan (SBP) tightening Technology Risk Management frameworks and a permanent shift toward hybrid work across Karachi, Lahore, and Islamabad, the old way of securing data, the VPN, is no longer sufficient.
At Ambsan Technologies, we are helping organizations transition from legacy infrastructure to a modern, identity-centric posture. This guide explores why the shift from VPNs to Zero Trust Network Access (ZTNA) is the most critical move for Pakistani enterprises this year.
The Sunset of the VPN: Why It’s Failing Pakistani Businesses
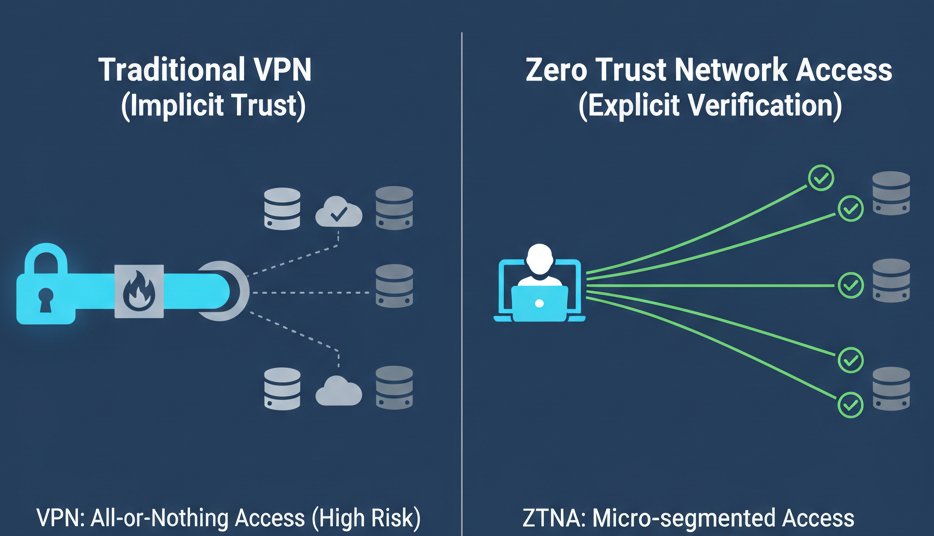
For decades, the Virtual Private Network (VPN) was the “gold standard.” It created an encrypted tunnel from a remote laptop to the office server. However, in the 2026 threat landscape, this model has three fatal flaws:
1. The “All-or-Nothing” Access Problem
A VPN is like a physical key to your front door. Once a user is “in,” they are on the network. If a hacker steals a single employee’s VPN credentials, they can move laterally through your entire infrastructure, from HR records to financial databases. In a country where credential-based phishing is the #1 cyber-attack vector, this “implicit trust” is a ticking time bomb.
2. The Performance Bottleneck (Latency)
Most Pakistani enterprises “hairpin” their traffic, meaning a remote worker in Islamabad accessing a cloud app in Singapore must first send their data back to a central server in Karachi. This creates massive latency, frustrating employees and slowing down productivity.
3. The Growing Attack Surface
VPN gateways are public-facing. They sit on the open internet, waiting for connections. This makes them easy targets for DDoS attacks and automated vulnerability scanners used by global ransomware syndicates.
What is ZTNA? (The Zero Trust Advantage)
Zero Trust Network Access (ZTNA) operates on a simple but powerful principle: “Never Trust, Always Verify.”
Unlike a VPN, which grants access to a network, ZTNA grants access to specific applications. When an employee at a bank or a software house in Pakistan tries to access a file, ZTNA doesn’t just check their password. It checks:
- Identity: Is this really the user? (Verified via MFA).
- Device Health: Is the laptop encrypted? Is the antivirus running?
- Context: Is it normal for this user to log in at 2:00 AM from a new IP address?
4 Key Reasons Pakistan’s Enterprises are Switching to ZTNA
1. Alignment with SBP & Regulatory Frameworks
The State Bank of Pakistan’s 2025-2026 Technology Risk Management Framework now explicitly requires “risk-based security controls” and “granular access management.” ZTNA is the most direct path to compliance, providing the exact audit trails that regulators demand.
2. Elimination of Lateral Movement
In a ZTNA environment, applications are “dark.” If a user is authorized to see the CRM, they cannot even see the Finance server on the network. This effectively stops ransomware in its tracks; the “blast radius” is contained to a single app.
3. Superior User Experience for Hybrid Teams
ZTNA connects users directly to the application, whether it’s on-premise or in the cloud. No more “connecting to the VPN” and waiting for the tunnel to stabilize. It’s seamless, fast, and works in the background.
4. Scalability for “Cloud-First” Strategies
As more Pakistani firms migrate to AWS, Azure, or local cloud providers, ZTNA scales effortlessly. You don’t need to buy more expensive VPN concentrators; you simply update your cloud-based access policies.
The Ambsan Roadmap: How to Modernize without Downtime
Transitioning to Zero Trust doesn’t mean “ripping and replacing” everything on day one. At Ambsan Technologies, we follow a proven 4-step migration path:
- Identity Audit: We consolidate your users into a single identity provider (like Microsoft Entra ID or Okta) and enforce Multi-Factor Authentication (MFA).
- Application Mapping: We identify your “Crown Jewels”, the critical apps that need protection first.
- Pilot ZTNA Deployment: We set up a Zero Trust gateway for a specific department (e.g., Finance or DevOps) to prove the model without disrupting the whole company.
- Phased VPN Decommissioning: As more apps move to the ZTNA model, we gradually turn off the legacy VPN, shrinking your attack surface until it’s gone.
Conclusion: Don’t Let Your Perimeter Be Your Weakest Link
The “moat and castle” era of cybersecurity is over. In 2026, your employees are working from home, in cafes, and on the move. Protecting them requires a strategy that follows the User, not the Network.
Moving from VPN to ZTNA isn’t just a technical upgrade, it’s a business necessity to ensure resilience, compliance, and speed.
Is your organization still relying on legacy VPNs?
Contact Ambsan Technologies today for a comprehensive Secure Remote Access Audit. Let our experts show you how to build a Zero Trust architecture that secures your digital future.
