When a cyberattack strikes, the pressure to recover quickly can lead to serious missteps. While detecting and containing the attack is critical, the recovery phase is where many organizations go wrong, often unintentionally. These mistakes can prolong downtime, increase financial losses, and even leave systems vulnerable to repeat attacks.
In this blog, we’re breaking down the most common cyberattack recovery mistakes companies make during cyberattack recovery. Understanding them is the first step toward building a smarter, more resilient response strategy.
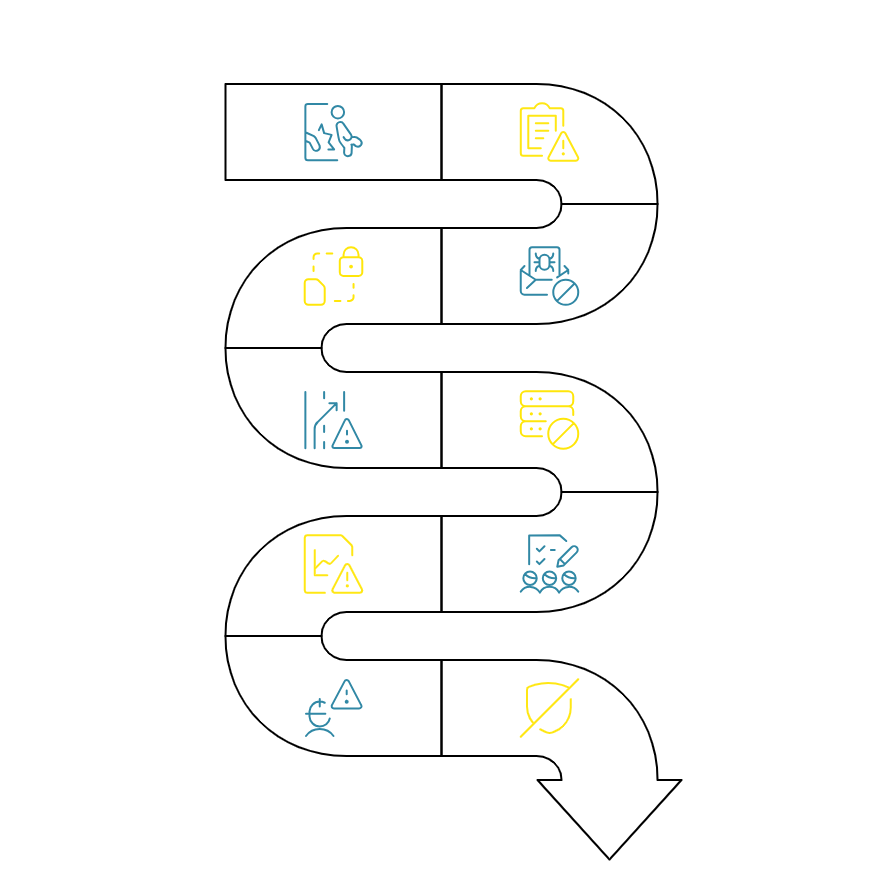
1. Rushing to Restore Systems
After a cyberattack, the pressure to get operations back online can be overwhelming. Systems are down, customers are frustrated, and business leaders want answers, fast. In this chaos, many organizations fall into the trap of restoring systems too quickly, without fully understanding the scope or depth of the breach.
This reaction is understandable, downtime equals lost revenue, reputational damage, and growing stress across departments. But acting hastily during this critical phase can backfire.
When teams rush into recovery mode, they may:
- Overlook hidden malware still lurking in the system.
- Restore compromised configurations or applications.
- Miss key forensic data that could help identify the attacker or method of entry.
In some cases, this can lead to re-infection, or even give attackers a second chance to strike , especially if their access was never fully removed in the first place.
Worse, systems might be restored to a vulnerable state, replicating the exact same conditions that enabled the initial attack.
The result? Recovery efforts stretch longer than necessary, and the business faces repeated disruptions, sometimes worse than the first.
2. Skipping Forensic Analysis
In the urgency to bounce back after a cyberattack, many organizations skip one of the most critical steps: forensic analysis.
Instead of pausing to understand how the attack happened, what was affected, and who was behind it, the focus immediately shifts to system restoration and damage control. While understandable, this approach can be dangerously shortsighted.
Skipping a thorough forensic investigation means:
- The root cause of the breach may never be identified.
- There’s no clear visibility into what data was accessed, stolen, or altered.
- Hidden backdoors or malicious code left by attackers might go undetected.
- Legal, compliance, and regulatory reporting may be incomplete or inaccurate.
Even worse, without proper analysis, organizations have no way of knowing if the threat is truly gone or just waiting to resurface under a new disguise.
In many high-profile breaches, it’s been forensic teams, not IT departments, who uncovered the full extent of compromise, sometimes weeks or months after the initial recovery was declared “complete.”
Failing to perform this analysis not only increases the risk of future incidents but also erodes trust among stakeholders who expect transparency, accountability, and diligence in handling cyber crises.
3. Restoring from Infected Backups
One of the most overlooked and ironically, most damaging mistakes during cyberattack recovery is restoring from infected backups.
When disaster strikes, backups are supposed to be the safety net. But if those backups were created after the system was compromised, they might carry the same malware, backdoors, or corrupted files as the original environment.
In the rush to recover, many teams assume their backup data is clean. They initiate restoration without verifying the integrity of the backup effectively reinstalling the attacker’s access right back into the network.
This can lead to:
- Reinfection loops where the same malware keeps reappearing.
- A false sense of security, causing teams to miss ongoing threats.
- Delays in full recovery, as new infections continue to surface.
- Increased operational costs and repeated business disruptions.
In some cases, attackers intentionally corrupt backups or leave behind stealthy payloads, knowing that organizations will eventually rely on them in a recovery scenario.
Using compromised backups turns what should be a controlled, confident recovery into a cyclical crisis, often worse than the original breach.
4. Ignoring Endpoints and Devices
In the aftermath of a cyberattack, most of the attention typically goes to restoring central servers, databases, or cloud platforms. However, this leaves a critical blind spot: endpoints.
Endpoints such as laptops, desktops, smartphones, tablets, and even IoT devices often serve as entry points for attackers. Yet during recovery, these are frequently overlooked or given only a superficial inspection.
This mistake can be costly.
When endpoints are ignored:
- Compromised devices can continue to operate as silent threats, unknowingly harboring malware.
- Attackers may still have remote access via tools installed on individual machines.
- Malware can easily spread laterally back into the restored network, causing repeat infections.
In many cases, employees may reconnect personal or work devices to the network after recovery, unknowingly reintroducing the very threats the team worked to eliminate.
This creates a dangerous situation where IT teams believe the crisis is over while the threat remains very much alive, just moved to a quieter corner of the network.
Failing to address endpoints thoroughly in the recovery phase allows cybercriminals to maintain a foothold in your environment and potentially launch a second wave of attacks when defenses are down or focus has shifted.
5. Poor Internal and External Communication
In the wake of a cyberattack, clear, timely communication is often one of the first things to fall apart. While IT teams are busy containing the damage and restoring operations, communication with employees, customers, partners, and even regulators is frequently delayed, inconsistent, or completely overlooked.
This communication gap can have serious consequences.
Internally, when teams don’t receive clear updates:
- Confusion spreads quickly across departments.
- Employees don’t know how to respond to customer concerns or media queries.
- The lack of direction can lead to misinformation, panic, or accidental interference in recovery efforts.
Externally, the damage can be even worse:
- Customers feel left in the dark and may lose trust in the brand.
- Business partners question the company’s reliability or security posture.
- Regulators may impose penalties for non-disclosure or late breach notifications.
Silence or worse, mixed messages during a crisis often creates a perception of negligence, even if the technical response is well-handled. In some cases, companies face more backlash for how they communicated (or didn’t) than for the breach itself.
Effective communication isn’t just a PR concern it’s a critical component of cyberattack recovery. Mishandling it can escalate reputational damage and complicate an already sensitive situation.
6. Treating It as an IT-Only Problem
One of the most common and most damaging assumptions during cyberattack recovery is that only the IT department needs to be involved. While IT and security teams are on the front lines of containment and restoration, a cyberattack affects the entire organization, not just its systems.
When recovery is handled solely by IT:
- Legal risks may be overlooked, such as data privacy violations or breach reporting deadlines.
- Communication breakdowns occur because marketing, PR, or HR teams are left out of the loop.
- Leadership may not fully understand the business impact, delaying strategic decisions.
- Customer-facing teams remain uninformed, creating inconsistencies in messaging or service delivery.
A cyberattack isn’t just a technical event , it’s a business crisis. It affects operations, revenue, compliance, reputation, and stakeholder trust. Treating it as an IT-only issue leads to siloed thinking, slower decision-making, and misalignment across departments when unity is most needed.
Recovery demands a cross-functional approach, yet many organizations don’t realize this until after they’ve suffered through a fragmented, chaotic response.
7. Forgetting to Review What Went Wrong
Once systems are back online and operations resume, many organizations make the mistake of closing the chapter too soon. The adrenaline fades, teams breathe a sigh of relief and the post-incident review never happens.
This is a major lost opportunity.
Failing to review what went wrong means:
- The root causes of the incident may remain unaddressed.
- Gaps in detection, response, or communication are never identified or fixed.
- The same missteps are repeated during future incidents.
- The organization misses a valuable chance to improve its cyber resilience.
Without a structured review process, it’s easy for teams to revert to business as usual assuming the problem is over just because the symptoms are gone. In reality, many of the underlying vulnerabilities still exist.
Additionally, skipping the review can hurt employee morale. Teams that worked tirelessly to contain the crisis may feel their efforts weren’t acknowledged or learned from.
Cyberattacks are teachable moments but only if we take the time to learn.
8. Underestimating the Long-Term Damage
A common and dangerous misconception in cyberattack recovery is that once the systems are back up and running, the crisis is over. In reality, that’s often just the beginning of a longer and more complex aftermath.
The true impact of a cyberattack can unfold over weeks, months, or even years.
When organizations underestimate the long-term effects, they often:
- Overlook delayed legal consequences, such as lawsuits or regulatory fines.
- Miss the slow erosion of customer trust and loyalty.
- Fail to account for reputational harm that affects partnerships and public perception.
- Neglect the emotional and psychological toll on employees, especially those in high-pressure roles during the incident.
There’s also a financial layer to this mistake. Hidden costs like forensic investigations, brand repair, customer attrition, and extended downtime can pile up long after the initial breach.
Some companies even suffer secondary attacks, either due to lingering vulnerabilities or because threat actors see them as easy targets post-breach.
Assuming the damage is short-lived not only hinders proper recovery, it puts the organization at risk of being blindsided again.
9. Neglecting Customer Confidence
In the chaos of recovering from a cyberattack, many organizations become inward-focused prioritizing system restoration, damage control, and internal coordination. While these are essential, failing to manage customer confidence during and after the incident can cause long-lasting harm.
Customers expect transparency, accountability, and assurance that their data and trust are valued. When communication is vague, delayed, or missing entirely, it creates uncertainty and uncertainty breeds distrust.
Neglecting customer confidence can result in:
- Loss of business, as customers switch to competitors they perceive as safer.
- Brand damage, amplified by negative word-of-mouth or media coverage.
- Legal fallout, especially if affected users weren’t notified as required by law.
- A lingering reputation problem that impacts future sales, partnerships, and growth.
Customers don’t just judge a company by whether it was attacked they judge by how the company responded. Silence, denial, or generic statements can often do more damage than the breach itself.
Trust is fragile. Once broken, it’s difficult and costly to rebuild.
10. Not Updating Security Posture Post-Attack
One of the most critical yet surprisingly common mistakes organizations make after a cyberattack is assuming that restoring systems means the security posture is fine. Once operations resume, many businesses simply revert to the same configurations, processes, and security controls that existed before the incident.
This creates a dangerous false sense of security.
When organizations don’t update their security posture after an attack, they risk:
- Leaving vulnerabilities unpatched, allowing attackers or copycats to exploit the same weaknesses again.
- Keeping outdated policies, procedures, or tools that failed to detect or prevent the original attack.
- Missing opportunities to strengthen defenses with insights gained during the incident.
- Sending a message to attackers that the organization is an easy target, because nothing meaningful has changed.
Without deliberate efforts to adapt and evolve security measures, companies set themselves up for repeated compromises sometimes by the same threat actors.
In the end, a cyberattack should be a catalyst for meaningful improvement, not just a temporary disruption to business as usual.
Conclusion
Recovering from a cyberattack is more than just restoring systems it’s about protecting your business from future threats, rebuilding trust, and learning from what went wrong. Yet, many organizations unknowingly make avoidable mistakes that leave them exposed to repeat incidents, financial losses, and long-term reputational damage.
At Ambsan, we understand that effective cyberattack recovery isn’t just technical it’s strategic. Whether you’re dealing with an incident now or want to strengthen your response capabilities, our experts are here to help you navigate every phase with confidence.
Don’t wait for the next breach to expose your weaknesses.
Contact Ambsan today to assess your cyber resilience and prepare your business for a secure, smarter recovery.
